Overcoming Edge Computing Challenges: Security, Scalability, and Beyond

| Tags: Edge Computing Challenges, Edge Security, Scalability Solutions, Tech Implementation 2025
Picture this: Your edge network is humming along, powering a fleet of autonomous drones delivering packages in under 30 minutes flat. Then, a cyber breach exposes sensitive location data, or a sudden surge in device connections crashes your local nodes. Edge computing’s promise of speed and decentralization is revolutionary—but it’s not without pitfalls. In 2025, as adoption skyrockets (IDC forecasts 50% of enterprises will deploy edge by year-end), ignoring these hurdles could turn innovation into a liability.
If you’re tracking our Exploring Edge Computing in 2025 series, you’ve seen the foundations in Edge Computing 101, architecture decisions in Edge vs. Cloud, and triumphs in Real-World Use Cases. Now, in Post 4, we roll up our sleeves to confront the tough stuff: security vulnerabilities, scalability snags, integration woes, and more. We’ll break down the risks, share battle-tested strategies from industry pros, and arm you with actionable steps to build robust edge ecosystems. No sugarcoating—just the roadmap to edge mastery.
Digital Fortress with Edge Nodes

The Big Four Challenges: What Keeps Edge Leaders Up at Night
Edge’s distributed nature amplifies traditional IT pains while introducing new ones. Distributed processing means more attack surfaces, varying hardware, and data gravity pulling in opposite directions. A 2025 Forrester report highlights that 60% of edge projects fail due to poor planning around these issues. But fear not—these are solvable with the right mindset and tools.
Let’s dissect the core challenges, complete with real-world pitfalls and fixes.
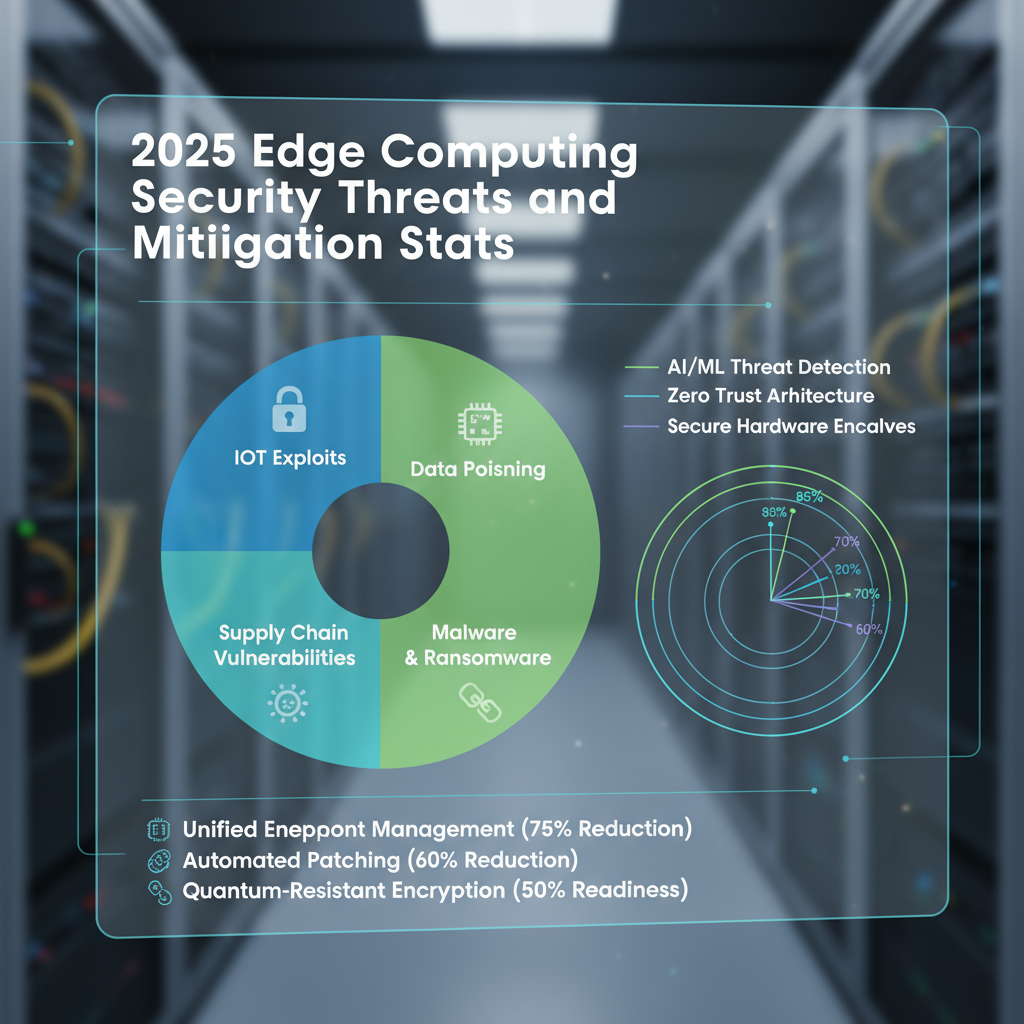
Challenge 1: Security in a Decentralized World
Edge devices—often in remote or exposed spots—are prime targets for breaches. Unlike centralized clouds with robust perimeters, edge nodes juggle unpatched IoT gadgets and sensitive data, risking everything from DDoS floods to ransomware.
Pitfall Example: The 2024 Retail Edge Hack
A major U.S. chain’s edge-enabled smart shelves were compromised via a vulnerable camera feed, leading to a $1.2M data leak and weeks of downtime. The root? Inconsistent firmware updates across 5,000+ endpoints.
Strategies for Ironclad Security
- Zero-Trust Architecture: Implement micro-segmentation with tools like Istio or Zscaler Edge. Assume every device is hostile—verify continuously. A logistics firm using this saw breach attempts drop 70%.
- Edge-Native Encryption: Use hardware-rooted keys (e.g., TPM chips in Intel’s latest edge processors) for data-at-rest and in-transit. In 2025, quantum-resistant algos like those in NIST’s post-quantum suite are must-haves.
- Automated Threat Hunting: Deploy AI-driven monitoring via platforms like Darktrace for Edge, which flags anomalies in milliseconds. Pro tip: Start with a security audit using OWASP’s edge guidelines.
For devs: Bake security in from day one with DevSecOps pipelines—scan containers before they hit the edge.
Security Threat Landscape
Challenge 2: Scalability Without the Overhaul
As your IoT footprint grows—from 1,000 to 100,000 devices—edge can bottleneck on resource contention or orchestration complexity. Clouds scale effortlessly; edge demands clever federation.
Pitfall Example: Manufacturing Scale-Out Gone Wrong
A European automaker’s edge rollout for factory sensors stalled at 10,000 nodes due to siloed clusters, causing 15% data loss during peaks and a $500K rework bill.
Strategies for Seamless Scaling
- Federated Edge Orchestration: Leverage Kubernetes-based tools like K3s or Open Horizon for lightweight, multi-site management. This allows dynamic resource pooling—scale nodes on-demand without full redeploys.
- Hybrid Edge-Cloud Bursting: Use gateways (e.g., AWS IoT Greengrass) to offload non-critical workloads to the cloud during spikes. A 2025 benchmark from Red Hat showed 3x faster scaling with this hybrid model.
- Containerization Everywhere: Standardize on OCI-compliant containers for portability. For hardware diversity, edge-specific runtimes like balenaOS handle ARM-to-x86 shifts effortlessly.
Business leaders: Model scalability with simulations—tools like EdgeX Foundry offer free PoCs to predict growth pains.
Scalable Edge Deployment

Challenge 3: Integration and Interoperability Headaches
Edge thrives on ecosystems, but mixing vendors (e.g., Siemens PLCs with Google Cloud IoT) often leads to protocol mismatches and data silos. In 2025’s multi-vendor reality, this fragments insights and inflates costs.
Pitfall Example: Healthcare Interop Fail
A U.S. clinic’s edge wearables couldn’t sync with legacy EHR systems, delaying patient alerts by hours and violating compliance—echoing a broader 40% failure rate in edge integrations per Deloitte.
Strategies for Frictionless Integration
- Standard Protocols First: Adopt MQTT or OPC UA for universal comms; they’re the lingua franca of edge in 2025. Bridge gaps with middleware like Eclipse IoT’s Californium.
- API-First Design: Expose edge services via RESTful APIs with GraphQL for flexible querying. Tools like Kong for edge API gateways ensure secure, scalable access.
- Low-Code Integration Platforms: Use no-code tools like Zapier for Edge or Flogo to connect disparate systems quickly—ideal for non-dev teams. A telehealth provider cut integration time from weeks to days.
Quick win: Audit your stack with the Edge Computing Consortium’s interoperability checklist.
Challenge 4: Management, Cost, and Skills Gaps
Beyond tech, edge demands ongoing ops: monitoring fleets, optimizing power (crucial for battery-powered edges), and upskilling teams. Costs can balloon if not monitored, with hidden fees for edge-specific compute.
Pitfall Example: Energy-Intensive Edge Flop
A smart agriculture project drained drone batteries 2x faster than planned due to unoptimized AI inference, scrapping the pilot and wasting $300K.
Strategies for Efficient Management
- Unified Observability: Centralize with Prometheus + Grafana for edge metrics—track CPU, latency, and costs in one dashboard. In 2025, AI ops tools like Moogsoft automate anomaly fixes.
- Cost Optimization Frameworks: Tag and allocate resources with FinOps principles adapted for edge (e.g., via CloudHealth). Aim for 20-30% savings by rightsizing nodes.
- Upskilling Pathways: Certs like Certified Edge Professional (from LF Edge) bridge gaps. Start with internal hackathons to build buy-in.
For sustainability: Prioritize green edge chips (e.g., Arm’s low-power Neoverse) to cut carbon footprints by up to 50%.
[Comparison Chart Placement: Challenge vs. Solution Matrix]
(Alt Text: “Edge computing challenges and strategic solutions overview.” Drop in a clean table here: Columns for Challenge, Risk Level, Top Tools, and ROI Boost—e.g., Security | High | Zero-Trust | 70% threat reduction.)

| Challenge | Risk Level | Key Tools/Strategies | Expected ROI Boost |
|---|---|---|---|
| Security | High | Zero-Trust, Edge Encryption | 70% fewer breaches |
| Scalability | Medium | Federated Orchestration, Hybrid Bursting | 3x faster growth |
| Integration | High | MQTT/OPC UA, API Gateways | 50% less downtime |
| Management/Cost | Medium | Observability Dashboards, FinOps | 25% cost savings |
Key Takeaways: Turning Challenges into Competitive Edges
Edge computing’s hurdles are real, but they’re also your opportunity to differentiate. By prioritizing security, scaling smartly, integrating thoughtfully, and managing proactively, you’ll not only mitigate risks but amplify gains—like the 35% efficiency jumps seen in resilient deployments.
Remember: Start with a maturity assessment (try Gartner’s Edge Scorecard). Pilot fixes in a sandbox, measure with KPIs (e.g., MTTR under 5 mins), and iterate.
[Call-to-Action Visual Placement: Roadmap Infographic]
(Alt Text: “Step-by-step roadmap to overcoming edge computing challenges.” Place an interactive flowchart at the end of takeaways—clickable steps from “Assess” to “Scale” for reader engagement.)
Looking Ahead: The Future of Frictionless Edge
We’ve tackled the thorns—now imagine thornless edge: Secure, scalable, and integrated, powering everything from metaverse factories to global health nets. In our series finale, The Future of Edge: AI, 6G, and Beyond, we’ll gaze into 2030, exploring emerging tech synergies and investment trends.
Which challenge hits closest to home for your team? Share in the comments or tweet me [@YourHandle]. Catch up on Use Cases for inspiration, and subscribe—your edge journey just leveled up!
Need help auditing your edge setup? Grab our free checklist or book a strategy call. #EdgeChallenges #SecureEdge #Tech2025
Promotion Ideas: X post: “Edge computing: Love the speed? Conquer the challenges! Blog 4 dives into security & scalability fixes 📈 [Link] #EdgeComputing” with the matrix snippet.
